
Proxmox Virtual Environment (VE) and Red Hat Virtualization are two popular virtualization solutions designed to support organizations of varying sizes. Both are solid, dependable choices for virtualized architecture with... Read more »
Botnets (derived from “robot networks”) are networks of computers or devices that have been compromised by malware and are under the control of a remote attacker (often called a... Read more »
Ransomware-as-a-service (RaaS) is a pay-for-use subscription model on the dark web where developers license out malware to other parties to execute targeted ransomware attacks. RaaS is advertised on the... Read more »
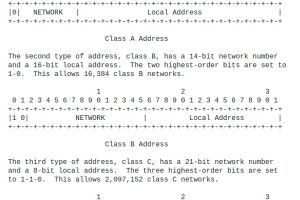
Classless Inter-Domain Routing (CIDR) is an IP addressing system that replaced the previous system of using Class A, B, and C networks. CIDR was developed to help alleviate the... Read more »

