
Source: Netgear and Cisco. Netgear and Cisco are leading manufacturers of ethernet switches, each with its own strengths. Netgear is known for its affordable and easy-to-use products, while Cisco... Read more »
Cybersecurity doesn’t sit still. No matter what practices your organization has put into place, it’s imperative to stay on top of evolving threats and implement effective defenses to protect... Read more »
While it is common for organizations to recognize the need to secure their networks, many still struggle with knowing what steps to take or where to start. In this... Read more »
Scareware is a type of malware that redirects people to malicious websites after they believe something’s wrong with their computer or mobile device. Cybercriminals developed scareware to capitalize on... Read more »
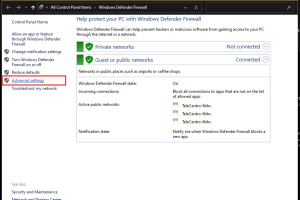
Like all other firewalls, Windows Defender Firewall acts as a barrier and gatekeeper, monitoring incoming and outgoing network traffic and allowing or blocking it based on security rules. Through... Read more »
Firewalls are essential to any robust cybersecurity strategy as they help organizations control inbound and outbound traffic, monitor for malicious activities, and protect their systems against unauthorized access. However,... Read more »

Enterprise firewall software is an essential component of network security infrastructure for organizations. These firewalls are designed to provide high availability and scalability to meet the needs of large... Read more »
Virtual memory is one of the most essential elements of an operating system (OS). Linux virtual memory works differently than other OS. Linux virtual memory uses different techniques, such... Read more »
Phishing is a social engineering tactic where hackers use fraudulent practices to collect sensitive data of users on the internet. Phishers acquire valuable details under the garb of anonymity... Read more »
Phishing awareness training is continued training given to employees to help them spot a phishing attack and take preventive measures when targeted. Worldwide, phishing attacks are one of the... Read more »

