Cloud is open. Or perhaps more accurately, many of the fastest growing and most widely deployed technologies currently playing out and evolving across the global cloudscape are open source. ... Read more »

Without a resilient network, all the processing power and memory of an infrastructure come to nothing. It is the network that establishes the internal and external connections to devices... Read more »
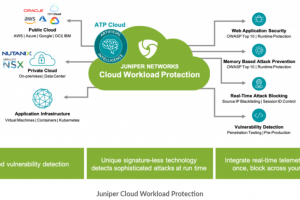
The advantages of migrating to the cloud are manifold. Capabilities like greater agility, higher resilience, and lower costs enable businesses to get ahead of the curve. As organizations transition... Read more »
As AI technology continues to advance, enterprise businesses need to learn the top three ways to effectively implement AI as a service. Artificial intelligence (AI) has increasingly moved to... Read more »
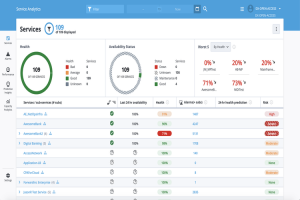
Artificial Intelligence for IT Operations (AIOps) platforms are multilayered tools that enhance information technology (IT) operations and provide automation by using machine learning (ML) and analytics to analyze big... Read more »
Intent-based networking is being touted as the next big thing in IT (information technology) networking, with companies from a variety of industries already starting to deploy it in their... Read more »
As major players in the tech world continue to invest in the future of the metaverse, the skepticism behind its practicality for enterprise businesses is starting to wither away.... Read more »
Juniper Networks is rolling out a program aimed at helping enterprises handle the rapidly growing numbers of Internet of Things (IoT) devices that are coming into their IT environments,... Read more »
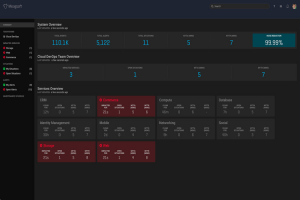
Artificial Intelligence for IT Operations (AIOps) is the application of technologies like artificial intelligence (AI), machine learning (ML), and natural language processing (NLP) to traditional IT operations (ITOps) tasks... Read more »

Cloud security posture management (CSPM) encompasses the methods, tools, and practices by which an organization protects data in cloud storage from security threats. As more and more companies use... Read more »

