Information is one of any company’s most prized possessions, and when attackers know that you have valuable data, they will try anything to get it. Social engineering refers to... Read more »
Cybersecurity hiring is facing a skilled labor shortage as companies undergo digital transformation and need more cybersecurity professionals than the current labor market can provide. Over the past two... Read more »
As cyber attacks become more sophisticated and happen more frequently, SBOMs or software bills of materials have become a more common practice across the software supply chain to trace... Read more »
An application programming interface (API) is a set of rules and specifications that govern how two applications can interact, usually over the internet. API is also known as an... Read more »
Despite the rise of low-code/no-code software platforms and the efforts laid down by top-tier software vendors to simplify their expanding product portfolios, the general trend that surfaces across the... Read more »
5G, or the fifth generation of cellular networks and technologies, is quickly spreading worldwide but does not yet have a public foothold in most global communities. Enterprises know they... Read more »
Smart buildings and factories, connected cars, wearables—all of these are part of a growing ecosystem that promises a smarter way to live. At one time, as simple tools used... Read more »
Over the last half-century, networks have changed through a number of different connectivity eras (client-server and more) and platforms, processes, and procedures have evolved in line with current trends... Read more »
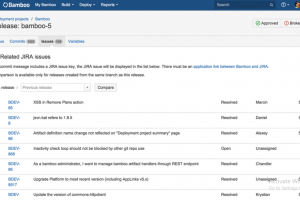
Bamboo and Jenkins are popular automation servers with plugins to support continuous integration. Although they share a few features, they differ from each other enough to make it easy... Read more »
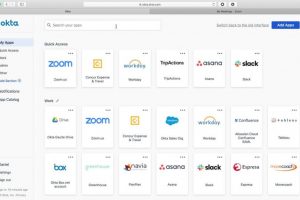
What is Identity and Access Management? It is critical to make sure that the correct resources are accessed by the appropriate people in disparate technology environments and ensure that... Read more »

