Internal Border Gateway Protocol (iBGP) is a routing protocol used on the internet for exchanging routing information between two or more routers within an autonomous system (AS)—hence the use... Read more »

Avast and Norton are two of the most well-established antivirus providers in the market today. They both deliver effective tools for protection against malware and viruses, with additional tools... Read more »

Webroot and Bitdefender are a pair of popular antivirus solutions that deliver different approaches to securing devices. Webroot’s popularity stems from its exceptionally quick scans, while Bitdefender’s robust approach... Read more »

Ransomware attacks are a profitable business for cybercriminals and show no signs of diminishing. These attacks can cause data and financial loss as well as reputational damage to enterprises.... Read more »
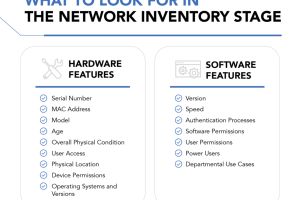
People often argue it’s impossible to prepare for or fight back against threats without knowing what they are. That understanding highlights the need for thorough and regularly performed network... Read more »
A flat network is a type of network architecture where all the devices in the data center can reach each other without having to go through intermediary devices like... Read more »
Border Gateway Protocol (BGP) is the protocol that connects all networks over the internet, allowing your computer to send and receive data from other computers located anywhere in the... Read more »
SQL injection (SQLi) is one of modern web applications’ most serious security threats. It enables malicious users to inject malicious code into a database to gain access to confidential... Read more »

Firewalls come in two standard types, stateful and stateless. Stateless firewalls check packets individually before deciding whether or not to permit them, while stateful firewalls are able to track... Read more »
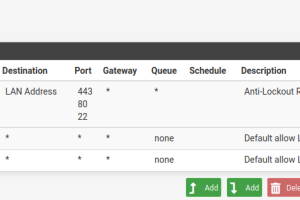
When it comes to online security, firewalls are an essential tool for protecting data and networks from malicious cyberattacks. A firewall is a system designed to control access between... Read more »

